Thoughts
Thoughts
SBOM is only step one
SBOM is only step one
The real role of SBOM is not to complete a compliance exercise, but to establish the inventory layer needed for faster vulnerability qualification and stronger software supply chain control.


You cannot monitor what you do not know exists. That is why SBOM, the Software Bill of Materials, matters: it provides the first structured view of what is inside a product. Yet adoption is still far from universal. Many buyers do not request SBOMs systematically, and less than 56% of software publishers produce them consistently for every release in 2025.
Its value remains poorly understood beyond engineering and product security teams. Buyers, operators, and procurement and GRC teams feel they are still lacking the software transparency they need to assess risk, coordinate action, and make informed decisions.
Cause SBOM-based inventory is not the destination. Better software supply chain control is. That means knowing what is affected within your software, understanding whether it truly matters, and sharing that answer with the right people fast. SBOM is the first necessary pillar. The next challenge is making it operational.
Making SBOM Operational
1. Anchor the Inventory
An SBOM is only useful if it stays tied to real product versions over time.
That means:
automatically generating SBOMs consistently for each release
storing them in a way that remains structured and accessible
linking each SBOM to the exact product version it describes
Standards such as SPDX and CycloneDX make that inventory structured, machine-readable, and usable across tools and teams.
Without that reference layer, software composition remains fragmented across engineering tools and internal knowledge. With it, software vendors, buyers and operators gain a reliable starting point for vulnerability tracking.
2. Contextualize
Inventory alone is not enough.
An SBOM tells you what is present. It does not tell you whether a known vulnerability actually affects the product in practice. That is why SBOM needs to be paired with VEX (Vulnerability Exploitability eXchange) and structured qualification data.
SBOM tells you what is inside the product
VEX tells you whether a known vulnerability affects that product or version in context
Recent CISA-led guidance makes this point clearly: organizations should rely on software vendor security advisories, ideally in automation-friendly formats, to determine whether a vulnerability actually makes the software exploitable.
Standards such as OpenVEX make that qualification explicit through statuses such as:
under_investigationnot_affectedaffectedfixed
3. Build a Vulnerability Knowledge Base
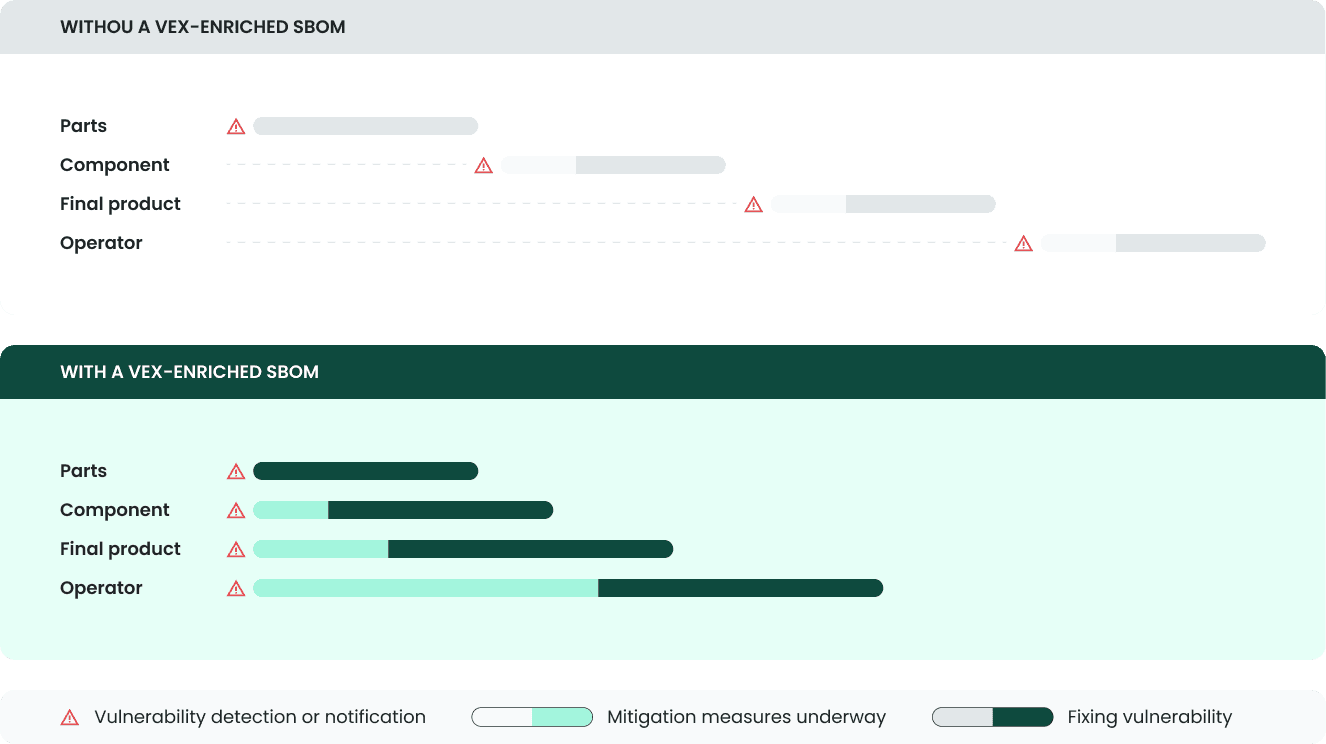
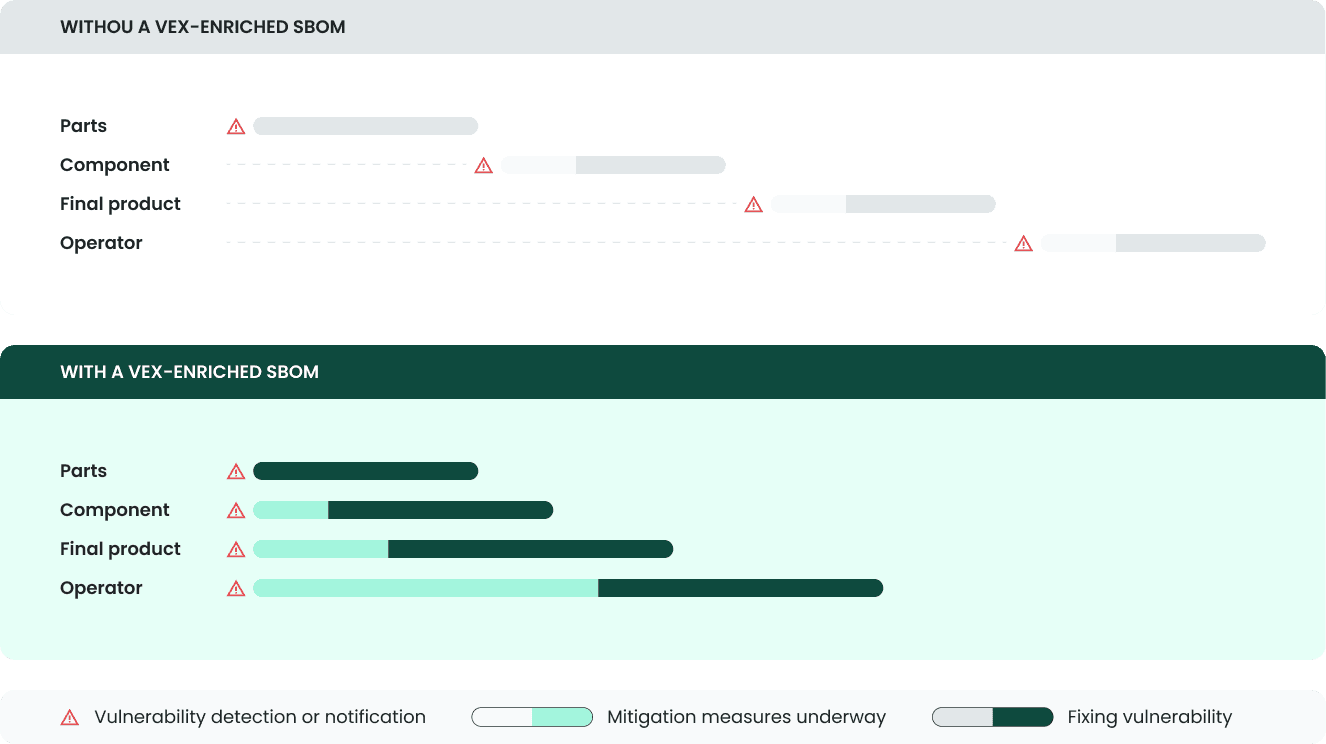
Once SBOM is maintained across releases and paired with VEX, it stops being a static artifact. It becomes a living knowledge base of product vulnerability status for software vendors’ internal teams and their customers. Without VEX, the interpretation burden stays downstream.
That is what makes SBOM fully operational:
recurring analysis against new vulnerability intelligence
clear qualification of new scan results
a shared view across engineering, product security, support, and customer-facing teams
With this, we build a reliable knowledge layer that supports qualification, communication, and action over time. Together, SBOM and VEX create the foundation for real software supply chain risk management.
SBOM: a global software supply chain topic
Operational SBOM is not only a software vendor problem. It is a global supply chain problem.
Operational SBOM for software vendors
SBOM provides the foundation for a universal knowledge layer across their product portfolio. It creates structured visibility across versions, components, and dependencies, and makes that knowledge usable beyond engineering. Product security, support, compliance, and other customer-facing teams all benefit from working from the same inventory and the same qualification layer.
Operational SBOM for buyers
For buyers and operators, SBOM is just as important.
That matters at multiple levels.
IT and security teams: it reduces the time needed to understand whether a newly disclosed vulnerability affects deployed software, and whether remediation or mitigation is required. More broadly, it helps turn software risk from a black box into something that can actually be monitored and managed.
Procurement and GRC teams: VEX-enriched SBOM supports vendor oversight and helps verify whether contractual security clauses are being met, especially around notification obligations and response timelines.
Operational SBOM enables control and software supply chain risk reduction.
When participants across the supply chain share a structured inventory layer and pair it with clear qualification, the time needed to identify and respond to vulnerabilities can be reduced significantly.
This is exactly the problem Tacit is built to address.
Tacit helps software publishers turn SBOM from a static artifact into an operational layer thanks to its sharing network. It structures version-level inventory, supports recurring analysis over distributed software, and makes vulnerability qualification explicit through VEX.
SBOM is step one. But software supply chain control starts when that inventory becomes a living knowledge base for qualification, communication, and action.
You cannot monitor what you do not know exists. That is why SBOM, the Software Bill of Materials, matters: it provides the first structured view of what is inside a product. Yet adoption is still far from universal. Many buyers do not request SBOMs systematically, and less than 56% of software publishers produce them consistently for every release in 2025.
Its value remains poorly understood beyond engineering and product security teams. Buyers, operators, and procurement and GRC teams feel they are still lacking the software transparency they need to assess risk, coordinate action, and make informed decisions.
Cause SBOM-based inventory is not the destination. Better software supply chain control is. That means knowing what is affected within your software, understanding whether it truly matters, and sharing that answer with the right people fast. SBOM is the first necessary pillar. The next challenge is making it operational.
Making SBOM Operational
1. Anchor the Inventory
An SBOM is only useful if it stays tied to real product versions over time.
That means:
automatically generating SBOMs consistently for each release
storing them in a way that remains structured and accessible
linking each SBOM to the exact product version it describes
Standards such as SPDX and CycloneDX make that inventory structured, machine-readable, and usable across tools and teams.
Without that reference layer, software composition remains fragmented across engineering tools and internal knowledge. With it, software vendors, buyers and operators gain a reliable starting point for vulnerability tracking.
2. Contextualize
Inventory alone is not enough.
An SBOM tells you what is present. It does not tell you whether a known vulnerability actually affects the product in practice. That is why SBOM needs to be paired with VEX (Vulnerability Exploitability eXchange) and structured qualification data.
SBOM tells you what is inside the product
VEX tells you whether a known vulnerability affects that product or version in context
Recent CISA-led guidance makes this point clearly: organizations should rely on software vendor security advisories, ideally in automation-friendly formats, to determine whether a vulnerability actually makes the software exploitable.
Standards such as OpenVEX make that qualification explicit through statuses such as:
under_investigationnot_affectedaffectedfixed
3. Build a Vulnerability Knowledge Base
Once SBOM is maintained across releases and paired with VEX, it stops being a static artifact. It becomes a living knowledge base of product vulnerability status for software vendors’ internal teams and their customers. Without VEX, the interpretation burden stays downstream.
That is what makes SBOM fully operational:
recurring analysis against new vulnerability intelligence
clear qualification of new scan results
a shared view across engineering, product security, support, and customer-facing teams
With this, we build a reliable knowledge layer that supports qualification, communication, and action over time. Together, SBOM and VEX create the foundation for real software supply chain risk management.
SBOM: a global software supply chain topic
Operational SBOM is not only a software vendor problem. It is a global supply chain problem.
Operational SBOM for software vendors
SBOM provides the foundation for a universal knowledge layer across their product portfolio. It creates structured visibility across versions, components, and dependencies, and makes that knowledge usable beyond engineering. Product security, support, compliance, and other customer-facing teams all benefit from working from the same inventory and the same qualification layer.
Operational SBOM for buyers
For buyers and operators, SBOM is just as important.
That matters at multiple levels.
IT and security teams: it reduces the time needed to understand whether a newly disclosed vulnerability affects deployed software, and whether remediation or mitigation is required. More broadly, it helps turn software risk from a black box into something that can actually be monitored and managed.
Procurement and GRC teams: VEX-enriched SBOM supports vendor oversight and helps verify whether contractual security clauses are being met, especially around notification obligations and response timelines.
Operational SBOM enables control and software supply chain risk reduction.
When participants across the supply chain share a structured inventory layer and pair it with clear qualification, the time needed to identify and respond to vulnerabilities can be reduced significantly.
This is exactly the problem Tacit is built to address.
Tacit helps software publishers turn SBOM from a static artifact into an operational layer thanks to its sharing network. It structures version-level inventory, supports recurring analysis over distributed software, and makes vulnerability qualification explicit through VEX.
SBOM is step one. But software supply chain control starts when that inventory becomes a living knowledge base for qualification, communication, and action.